Russian hackers have learnt to extort money for locked iPhone

The exact number of hacked phones is unknown. The representatives of Apple declined to comment.
The attackers use the fact that in the new version of iOS 7 has become possible to block stolen smartphone that cannot be removed with help of a reset or flashing devices. If you want to use this feature, you must know the user‘s name (Apple ID, also known as e-mail address) and password.
Russian official’s threat to ban Twitter spurs fast backlash
 Comments on Friday by a top Russian telecoms official, suggesting that the country might soon block access to Twitter, met with a swift wave of condemnation — including from other government officials — providing a rare window into differences of opinion inside the Kremlin over how best to censor voices of dissent.
Comments on Friday by a top Russian telecoms official, suggesting that the country might soon block access to Twitter, met with a swift wave of condemnation — including from other government officials — providing a rare window into differences of opinion inside the Kremlin over how best to censor voices of dissent.
In an interview with a local newspaper Friday, Maxim Ksenzov, deputy head of the government’s telecommunications watchdog, Roskomnadzor, called Twitter a “political” tool that undermines the state’s authority. “We can block Twitter or Facebook tomorrow for several minutes,” Ksenzov said. “We do not see any risks in that.”
Read moreFSB uses SORM to spy on Russians
 Russian law gives Russia’s security service, the FSB, the authority to use SORM (“System for Operative Investigative Activities”) to collect, analyze and store all data that transmitted or received on Russian networks, including calls, email, website visits and credit card transactions.
Russian law gives Russia’s security service, the FSB, the authority to use SORM (“System for Operative Investigative Activities”) to collect, analyze and store all data that transmitted or received on Russian networks, including calls, email, website visits and credit card transactions.
SORM has been in use since 1990 and collects both metadata and content. SORM-1 collects mobile and landline telephone calls. SORM-2 collects internet traffic. SORM-3 collects from all media (including Wi-Fi and social networks) and stores data for three years. Russian law requires all internet service providers to install an FSB monitoring device (called “Punkt Upravlenia”) on their networks that allows the direct collection of traffic without the knowledge or cooperation of the service provider.
Read moreFollow global cyber attacks in real time on interactive map
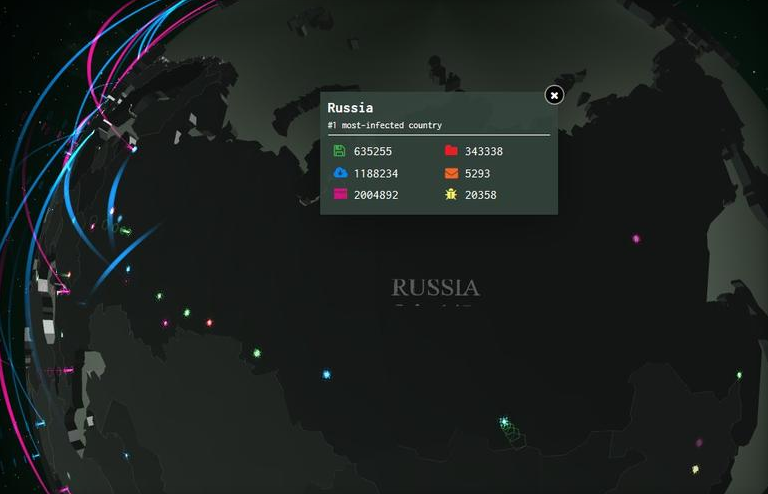 IT security vendor Kaspersky Lab realised “Cybermap" - a new online service to monitor violations of cyber security in real time. Company sees it as a strategic step - such a demonstration of online malware threats on a global level and in real time will serve as a great motivation to purchase their products.
IT security vendor Kaspersky Lab realised “Cybermap" - a new online service to monitor violations of cyber security in real time. Company sees it as a strategic step - such a demonstration of online malware threats on a global level and in real time will serve as a great motivation to purchase their products.
An interactive 3D globe shows locations of malware threats and active cyber attacks, as well as incidents of activations of mail and web antivirus software. All types of threats are classified and marked by colour - Kaspersky’s tools and experts process data for over 300 thousand threads daily.
Read moreSkype is forced to cooperate with Russian secret services
 Russian authorities put global communications providers on a tight leash demanding to gain access to users’ personal data and online correspondence.
Russian authorities put global communications providers on a tight leash demanding to gain access to users’ personal data and online correspondence.
A group of deputies representing all 4 political parties of State Duma presented a project of legislations aiming to support surveillance agencies to counter threats to national security.
A separate set of amendments forces telecommunication companies, including hosting providers and website owner to store data on “reception, transmission, processing and delivery of various electronic information” for the period of 6 months.
Read moreTelegram’s reputation as secure messenger is compromised?
 United Capital Partners, a Russian investor who holds 48% of VKontakte, the second largest social network service in Europe after Facebook, got involved into public discussion around an encrypted IM application Telegram.
United Capital Partners, a Russian investor who holds 48% of VKontakte, the second largest social network service in Europe after Facebook, got involved into public discussion around an encrypted IM application Telegram.
Supposedly UCP sent out a letter to Russian media companies describing in detail three negative scenarios for Pavel and Nikolai Durov, creators of Telegram, who also launched “VK” in 2006. The letter included copies of experts’ documents trying to prove that Telegram’s claim as a secure messenger is worthless. United Capital Partners officials refused their relation to the letter.
Read moreRussia’s Federal Security Service to take control over internet users
 Russia’s Federal Security Service (FSB) wants to gain maximum control over the information on the internet. This was reported today by Kommersant newspaper, which obtained access to a letter of VimpelCom, aimed at the Ministry of Communications. In the letter, the operator gives a number of comments on the draft ministerial order on investigative activities on the internet.
Russia’s Federal Security Service (FSB) wants to gain maximum control over the information on the internet. This was reported today by Kommersant newspaper, which obtained access to a letter of VimpelCom, aimed at the Ministry of Communications. In the letter, the operator gives a number of comments on the draft ministerial order on investigative activities on the internet.
In accordance with the draft order of the Ministry of Communications, from July 1, 2014 all internet providers are required to install network equipment for recording and storing internet traffic for minimum 12 hours, and the security forces will have direct access to these records.
Read moreGermany intensively targeted by U.S. surveillance programs
 Countries of greatest interest to the U.S. are China, Russia, Pakistan, Iran, North Korea and Afghanistan, according to German weekly.
Countries of greatest interest to the U.S. are China, Russia, Pakistan, Iran, North Korea and Afghanistan, according to German weekly.
The United States’ surveillance programs included intensive spying on Germany, the German weekly Der Spiegel reported on Saturday. Der Spiegel cited a classified document from the archive of Edward Snowden, the American citizen who fled the U.S. after revealing details of its espionage programs and has received temporary asylum in Russia. According to the report, in April 2013, U.S. officials ranked its espionage targets on a scale of 1 (of highest interest) to 5.
Read moreSkype raises eyebrows over security and wire-tapping
 The charge: Microsoft is reconfiguring the Skype network so that it Law Enforcement Agencies (LEA) can have access to intercept calls over the network to aid in investigations. The reality is of course convoluted with no concrete evidence but it’s worth mentioning what exactly is going on here. So head past the break to get the scoop.
The charge: Microsoft is reconfiguring the Skype network so that it Law Enforcement Agencies (LEA) can have access to intercept calls over the network to aid in investigations. The reality is of course convoluted with no concrete evidence but it’s worth mentioning what exactly is going on here. So head past the break to get the scoop.
As Rafael Rivera explained a few months ago is his article about Skype and Windows Phone, Skype’s original network operated on a peer-to-peer node system which means that Skype only initiated the calls but the actual communication was one-to-one with no one as the middleman.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















